
The Dark Side of APIs: What Went Wrong at T-Mobile & Honda

Last year breaches involving big names like T-Mobile and Honda have thrown this topic into sharp focus, and rightfully so.
Insecure APIs can expose sensitive customer data, leading to a nightmare of identity theft, phishing attacks, and reputational damage for your company.
Last year, we wrote that API Security is a top concern for businesses and organizations.
It seems like that behind the scenes there lies a dark and overlooked aspect of API Security.
Protect your APIs from threats with real-time security checks.
Treblle scans every request and alerts you to potential risks.
Explore Treblle
T-Mobile disclosed two data breaches in 2023, affecting millions of customers. The first breach, disclosed on January 19, 2023, impacted 37 million customers, while the second breach, disclosed on June 23, 2023, affected 836 customers.
Security researcher Eaton Zveare discovered two vulnerabilities in Honda's e-commerce platform for power equipment, marine, lawn & garden, which allowed unauthorized access to customer data and admin panels.
These incidents highlight the critical need for robust API security measures, proactive adoption of best practices, and timely response to security vulnerabilities to protect customer data and maintain a safe and trusted environment.
The incidents involving T-Mobile and Honda underscore the critical importance of API security. Businesses and developers must prioritize the security of their APIs to safeguard sensitive customer data. To delve deeper into the intricacies of API security, our article on the untold secrets of API security goes into detailed exploration.
Insecure APIs pose significant risks, including data breaches, financial loss, reputational damage, and legal implications, highlighting the urgent need for robust API security measures.
Here's why you should prioritize API security:
document every API in your ecosystem to gain a thorough understanding of the API landscape.tokens and certificates, for access, thereby mitigating unauthorized access and potential breaches.injection attacks and other vulnerabilities, enhancing the overall security posture of your APIs.HTTPS to encrypt all API traffic, safeguarding sensitive information from unauthorized access.regular penetration testing and security audits to identify and address weaknesses in APIs, thereby ensuring proactive mitigation of potential vulnerabilities.monitoring of API activity to track access patterns and detect anomalies that might indicate potential breaches, allowing for timely intervention and response to security threats.Protect your APIs from threats with real-time security checks.
Treblle scans every request and alerts you to potential risks.
Explore Treblle
To improve API security, businesses and developers should implement robust security measures such as API authentication, encryption, and access control.These measures help prevent unauthorized access and protect sensitive data from potential breaches.
Here are some key practices to fortify your API security:
Customer data is a valuable asset, and breaches due to insecure APIs can severely impact trust. A breach shakes that trust, potentially leading to customer churn and long-term damage to the business's reputation.
Data privacy regulations such as GDPR and CCPA carry substantial legal and financial consequences. Breaches resulting from insecure APIs can lead to hefty fines and reputational damage, making compliance a crucial aspect of API security.
Insecure APIs are a prime target for attackers, posing a significant risk of exposing vast amounts of customer data, as evidenced by the breaches at T-Mobile and Honda.
Treblle's API security solution provides a comprehensive shield for your APIs, safeguarding them from a wide range of threats.
Protect your APIs from threats with real-time security checks.
Treblle scans every request and alerts you to potential risks.
Explore Treblle
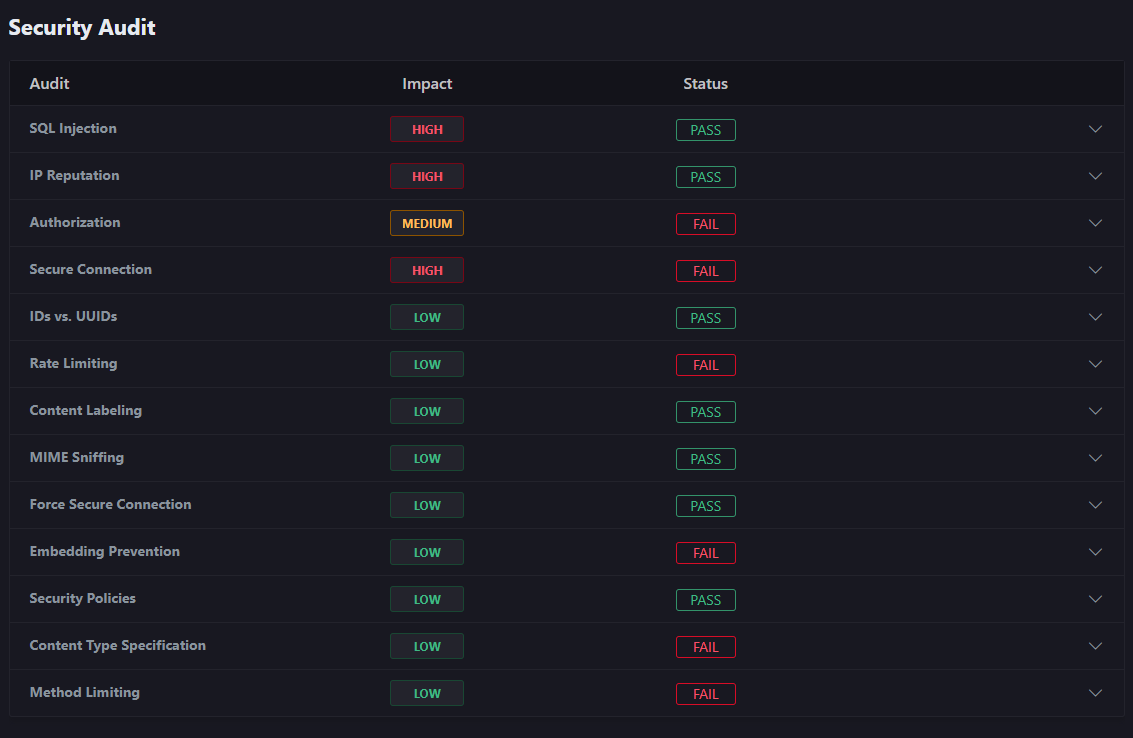
These checks identify vulnerabilities and categorize the request's threat level as low, medium, or high.
SQL injection patterns.own network as well as 3rd party services to check the reputation of your user's IP address.automatically detect all forms of authorization on every API request and check to make sure it's being used properly.automatically detects whether or not the requests your end customers are making are using HTTPs instead of HTTP.x-rate limit-* headers in the response payload to see if you correctly use rate limiting.Content-Type header exists and if its value is set to application/json.X-Content-Type-Options header exists and if its value is set to nosniff.strict-transport-security header in your API responses.X-Frame-Options header exists and its value is set to deny.Content-Security-Policy header defined.Accept header exists and if its value is set to application/json.Allow header exists.Core 15 Checks: Treblle automatically analyzes every single API request against 15 critical security checks.
API Traffic Spike Analysis: Treblle can evaluate the threat potential of sudden increases in API traffic volume. This helps identify potential denial-of-service attacks or other suspicious activity.
Treblle's API security solution caters to a wide range of industries and use cases:
By leveraging Treblle's automated security checks, real-time threat detection, and zero-trust approach, organizations across all sectors can significantly strengthen their API security posture and prevent data breaches like those experienced by T-Mobile and Honda.
Protect your APIs from threats with real-time security checks.
Treblle scans every request and alerts you to potential risks.
Explore Treblle
All Systems Operational
Gartner: Magic Quadrant, 2025
Gartner AI API Strategy, 2025
Everest Group: Enterprise App Integration Platforms, 2026